Cyber security solutions
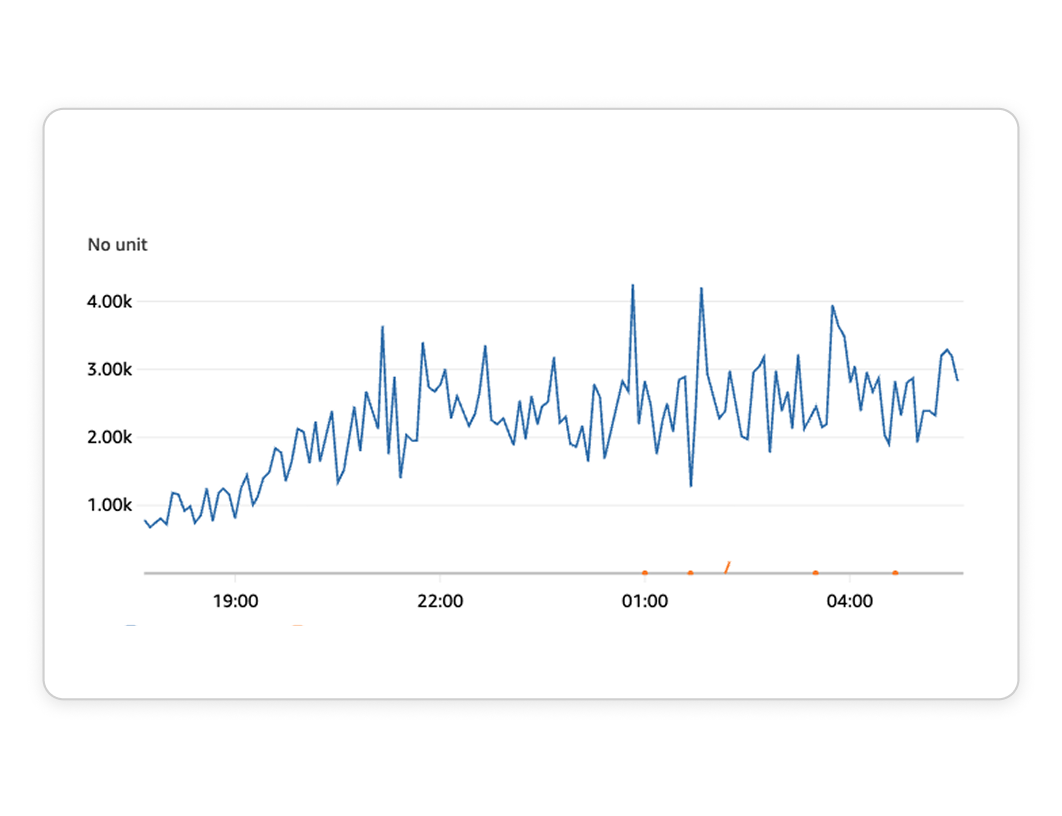
Protect your business with advanced cyber security solutions designed to secure your data and systems. Our approach combines proactive monitoring, security audits and network protection to reduce risk and give you greater peace of mind.

Protection with a managed security provider
In today’s digital landscape, online threats are constantly evolving, making effective cyber security essential. By partnering with a managed security provider, you can protect your data and systems while staying focused on core business activities, confident that your digital assets are being actively looked after.
Safeguarding sensitive data and intellectual property
Our proactive monitoring and incident response services provide continuous protection, addressing vulnerabilities as they appear. By protecting the systems and information your business relies on, we help you maintain client and partner trust while ensuring the stability of your day-to-day operations.
Supporting Australian organisations for over 20 years









Speak to an expert
Our cyber security solutions
Our cyber security services combine practical protection with expert guidance to help strengthen your digital infrastructure against attack. We begin by identifying vulnerabilities and developing targeted strategies to reduce risk so your systems and data stay protected. This creates a clear, manageable security framework that supports everyday operations and future plans alike.
Vulnerability assessment
Perform vulnerability assessments to detect and assess potential security flaws in your digital systems.
Cyber security consulting
Cyber security consulting to offer expert strategies and advice for improving your organisation’s security stance.
IT and technical support
IT and technical support for network and system issues, providing prompt resolutions.
Partnering with reliable cyber security experts
We offer an extensive range of cyber security services through trusted partners in cyber security, designed to meet the needs of small and medium-sized businesses. Our solutions focus on protection where it’s most needed, and we can also support you with compliance, auditing and the certifications required to meet and maintain industry or government standards.
Using the Essential 8 maturity checklist for compliance and resilience
Implementing the Essential 8 framework is an important step in protecting your organisation from cyber threats, and our team provides hands-on support to put these strategies into practice. We begin with a detailed review of your current security posture to identify gaps and opportunities for improvement. Using the Essential 8 maturity model, we then help you work towards compliance and strengthen your overall cyber resilience.
Our implementation work covers key areas such as application control, patch management and user access management. For access management, we set up strong authentication and tighten user permissions to reduce the risk of insider threats. We also offer ongoing support and monitoring so the Essential 8 controls remain embedded in your day-to-day operations, rather than being a one-off exercise.
Developing ISO 27001 policies and controls
Achieving ISO 27001 certification demonstrates your commitment to managing information security in a structured way. Our team can support you through every stage of the process, from initial gap analysis through to audit preparation. We help develop and implement the policies, procedures and controls needed to meet ISO 27001 requirements. With our guidance, you can gain and maintain this internationally recognised certification with confidence, ensuring your information security management system is both effective and efficient.
Strengthening your cyber security with CIS Controls
Incorporating CIS Controls into your cyber security strategy helps strengthen your defence against digital threats. Our team provides end-to-end support to help you adopt and apply these best-practice guidelines effectively. We work with you to review your current security measures, identify gaps and develop a clear roadmap for integrating the CIS Controls. By focusing on key areas such as asset management, vulnerability management and incident response, your organisation becomes better equipped to prevent, detect and respond to cyber threats.
Frequently asked questions
What are cyber security solutions?
Cyber security solutions are a set of practices, tools and technologies designed to protect your digital assets – including data, networks, and systems – from cyber threats such as hacking, malware, phishing and data breaches. These solutions can range from firewalls, antivirus software and encryption to more advanced measures like intrusion detection systems, multi-factor authentication and security information and event management (SIEM). The goal of cyber security solutions is to safeguard your organisation’s sensitive information, ensure compliance with data protection regulations, and maintain the integrity and availability of your systems.
Is the Essential 8 important for cyber security?
Yes, the Essential 8 is critically important for cybersecurity. Developed by the Australian Cyber Security Centre (ACSC), the Essential 8 provides a set of fundamental strategies designed to protect organisations from the most common and impactful cyber threats. By implementing these strategies, businesses can significantly reduce their risk of data breaches, ransomware attacks and other cyber incidents. The Essential 8 is especially important because it offers a practical, prioritised approach to cybersecurity, making it easier for organisations of all sizes to strengthen their defences and maintain a strong security posture. To learn more about the Essential 8 framework, contact our cybersecurity Essential 8 partners.
Does your business provide IT support services?
We offer comprehensive business support services in partnership with our trusted IT support partners, ensuring coverage across the entire Australian region. In key urban centres, we provide round-the-clock IT assistance to keep your business functioning seamlessly. Our partners are adept at managing an extensive array of IT tasks, from regular maintenance and issue resolution to sophisticated technical support and system oversight. Whether you need on-site service or remote assistance, our expert network is committed to delivering prompt and efficient solutions, ensuring your IT systems are always secure and effective.

Learn more about our cyber security solutions today
Get in touch for a technical assessment, security certification or simply to explore how our cyber security services can safeguard your business from emerging threats and vulnerabilities.
